Document Security Analysis That Actually Stops Real-World Breaches
It’s easy to believe your organization’s sensitive documents are locked down, firewalled, and immune to breaches—but that’s a dangerous illusion. The reality is far messier. Document security analysis isn’t a boardroom talking point; it’s a brutal, ongoing test of your defenses, your processes, and, frankly, your people. The stakes have never been higher: Data breaches exposed a jaw-dropping 7 billion records in the first half of 2024 alone, and document fraud is surging despite our best technological efforts. If you think the biggest threats are faceless hackers in distant lands, think again. Most failures happen in plain sight: overlooked permissions, lazy workflows, and misplaced trust. This article strips away the corporate politeness and unpacks seven brutal truths every leader must confront. We’ll navigate the evolution of document security, shatter persistent myths, dissect infamous breaches, and arm you with a modern playbook—complete with actionable steps, chilling case files, and the hard lessons insiders wish they’d learned sooner. Welcome to the real world of document security analysis—where ignorance isn’t bliss; it’s your next headline.
The evolution of document security: From locked drawers to AI guardians
Why document security analysis matters more than ever
Document security analysis has become a non-negotiable in the era of rampant data breaches and proliferating privacy laws. As organizations digitize everything from contracts to patient records, the risk landscape has exploded. A 2024 report found that global privacy regulations jumped by 45% in just one year, forcing companies to automate compliance and rethink every link in their document chain (PaperMark, 2024). Meanwhile, document fraud is evolving at a pace that outstrips many organizations’ ability to counteract it (SpringerLink, 2023). The consequences are brutal: In 2024, 38% of organizations lost business due to inadequate security—a stark but telling improvement from 67% the previous year (Exabeam, 2024). In short, ignoring document security analysis isn’t just naive; it’s reckless.
“Document security analysis is no longer an IT issue—it’s a business survival issue. Leadership ignoring this reality are inviting disaster.”
— Security Analyst, PaperMark, 2024
From paper trails to digital shadows: A brief history
The trajectory of document security is a study in reactive adaptation. In the analogue age, a locked filing cabinet and a vigilant admin sufficed. But as information moved online, threats multiplied, and so did the tools—encryption, watermarking, audit trails, and, eventually, AI-driven forensics. Yet, each advance brought new risks: convenience undermined control, and digital shadows replaced the paper trail, making unauthorized duplication and distribution almost frictionless.
| Era | Security Method | Key Vulnerability |
|---|---|---|
| Pre-2000s | Locked cabinets, stamps | Physical theft, forgery |
| 2000–2010 | Password-protected files | Weak passwords, shared access |
| 2010–2020 | Encryption, DLP, DRM | Insider leaks, phishing |
| 2021–2024 | AI analysis, blockchain | AI-powered attacks, deepfakes |
Table 1: The shifting landscape of document security across decades.
Source: Original analysis based on SpringerLink, 2023, PaperMark, 2024.
How the threat landscape exploded in the last decade
The past ten years have seen a seismic escalation in both attack techniques and damage. According to Varonis, the number of breached records in the first half of 2024 alone soared by 1,170% compared to the same period in 2023 (Varonis, 2024). Attackers are no longer just outsiders. Insiders—disgruntled employees, careless contractors—have become critical vulnerabilities. The tools have evolved: Generative AI now crafts convincing forgeries in seconds, while blockchain verification has surged 300% since 2021, reflecting desperate demand for trust in a trustless world.
Worse, the distinction between “document” and “data” is blurring, creating fertile ground for shadow IT, unsanctioned file sharing, and compliance nightmares. Organizations are scrambling to keep pace, pouring $87 billion into cybersecurity spend in 2024 alone—a sum that underscores both the gravity and scale of the challenge.
"The attack surface is no longer defined by your firewall; it's defined by every unsecured document, every careless workflow, and every untrained employee."
— Cybersecurity Lead, Exabeam, 2024
Breaking myths: What document security analysis is (and isn’t)
Debunking the ‘secure PDF’ illusion
If your organization is still sending “secure PDF” files and sleeping soundly, it’s time for a rude awakening. PDFs can be encrypted and password protected, but these defenses are often trivial to bypass. In reality, so-called “secure” documents are frequently cracked using free tools, exposing sensitive data to whoever wants it badly enough. According to recent research, the average time to remove PDF password protection is under 90 seconds for moderately skilled attackers (SpringerLink, 2023).
Most organizations vastly overestimate the security of common document formats. Watermarks offer deterrence, not defense; digital signatures can be spoofed; and access controls mean little when users forward files to personal accounts or cloud drives.
- “Secure” PDFs can usually be unlocked with free software or online tools, rendering their protection moot.
- Watermarks might deter casual leaks but do nothing to prevent determined criminals.
- Password protection is only as strong as your weakest user’s password habits—often, that means “1234”.
Document security vs. data security: The messy overlap
Organizations love to draw neat boxes around “document security” and “data security,” but the real world isn’t that tidy. Documents are just one container for sensitive data, and the lines get blurry fast.
Definition list:
Protection of the integrity, confidentiality, and authenticity of files (contracts, reports, etc.) throughout their lifecycle, from creation to destruction.
Broader practices and technologies aimed at safeguarding any data, structured or unstructured, in motion or at rest, regardless of format.
The messy truth: documents often contain structured data (like tables of client info), and data is often extracted from documents, making separate controls meaningless if not coordinated. This overlap drives demand for platforms like textwall.ai/document-analysis, which unify security, analysis, and compliance across both domains.
Red flags in vendor promises and marketing
Vendors flood the market with shiny promises, but the fine print hides uncomfortable truths. Every leader should watch for these telltale red flags:
- “Military-grade encryption” is meaningless without context or key management—ask for details, not buzzwords.
- “One-click compliance” solutions rarely account for unique nuances of your industry, location, or data types.
- “Set-and-forget” security is a myth; threats and regulations evolve too quickly for static solutions.
Be skeptical of blanket claims and push for evidence—like third-party audits, penetration tests, and transparent breach histories. Vendors that can’t provide specifics are gambling with your reputation.
Marketing is designed to soothe, not secure. Leaders who fall for platitudes end up surprised by leaks that “shouldn’t have been possible.” In document security, trust is earned with transparency and relentless verification.
Anatomy of a breach: How document security fails in the real world
Case study: The $60 million printout (and what went wrong)
Let’s get specific. In 2023, a global financial firm suffered a $60 million loss after a senior employee printed thousands of sensitive documents over several months without triggering a single alert. The breach wasn’t the work of a hoodie-wearing hacker—it was a trusted insider exploiting lax controls and ignored audit trails. Postmortem analysis revealed that while encryption and access controls were in place, print permissions weren’t monitored. The firm’s document security analysis failed because it focused on digital threats, not analog “leaks.”
The second failure? A lack of role-based access: too many employees had broad permissions, and document movement wasn’t tracked beyond the digital realm.
| Breach Element | What Failed | Consequence |
|---|---|---|
| Print permissions | Unmonitored | Mass exfiltration undetected |
| Role-based access | Overly broad | Insider exploited privileges |
| Audit trails | Not extended to physical docs | Post-breach forensics stymied |
Table 2: Dissecting the vulnerabilities in a real-world breach scenario.
Source: Original analysis based on Varonis, 2024, Exabeam, 2024.
An inside job: Why your biggest threat isn’t a hacker
Despite Hollywood’s fixation on shadowy outsiders, most document breaches start with someone on the inside. Disgruntled employees, careless contractors, or simply overwhelmed staff are responsible for the majority of leaks. According to Exabeam’s 2024 report, the prevalence of insider incidents remains stubbornly high despite increased investment in perimeter defenses.
“It’s not the hackers you see coming—it’s the trusted people you never suspect. The classic ‘it could never be my team’ blindness is what gets organizations burned.”
— CISO, Exabeam, 2024
From inbox to dark web: The invisible journey of a leaked document
Leaked documents don’t just vanish; they embark on a journey that’s both invisible and irretrievable.
- Email forwarding: A well-meaning employee forwards a sensitive report to their personal account for “convenience.”
- Cloud sync: That account is synced to an unsecured device—perhaps even a family tablet.
- Phishing attack: The device is compromised by malware, and the report is harvested by attackers.
- Dark web sale: The stolen document is listed for sale or auctioned on a dark web forum.
- Downstream fallout: Regulatory fines, reputational damage, and potential blackmail follow.
According to Varonis, 2024, 32% of major breaches involve data leaks that originated with a simple document mishandling. The journey of a leaked file is a winding road with more exits—and more risks—than most leaders care to admit. Document security analysis must map and defend every step, not just the obvious endpoints.
The new arsenal: Modern tools and strategies for document security analysis
Encryption, watermarking, and beyond: What actually works?
Not all document security tools are created equal. Encryption at rest and in transit is table stakes, but its effectiveness hinges on robust key management and user discipline. Watermarking can help track leaks but won’t prevent them. Blockchain verification has emerged as a potent tool for critical documents, offering immutable audit trails that make undetected tampering virtually impossible.
| Tool/Strategy | Strengths | Weaknesses |
|---|---|---|
| Encryption | Strong confidentiality | Key loss = data loss; user error |
| Watermarking | Leak tracing, deterrence | Easily removed by skilled actors |
| Digital signatures | Authenticity, non-repudiation | Can be spoofed if keys stolen |
| Blockchain watermark | Tamper-proof audit, traceability | Complexity, adoption hurdles |
| AI anomaly detection | Real-time risk alerts, deep analytics | False positives, ongoing tuning |
Table 3: Evaluating strengths and weaknesses of document security technologies.
Source: Original analysis based on PaperMark, 2024, SpringerLink, 2023.
AI-powered analysis: How textwall.ai and peers are shifting the game
AI-driven platforms like textwall.ai/ai-document-analysis are rewriting the rules of document security analysis. Using large language models, these tools can flag anomalous text, summarize lengthy contracts for risky clauses, and even detect suspicious metadata that would elude human reviewers. Real-time document intelligence is now providing organizations with 90% more actionable insights, per recent industry reports (PaperMark, 2024).
AI brings several new advantages:
- Pattern recognition at scale: Detects subtle deviations across thousands of documents in seconds.
- Automated content classification: Flags documents containing regulated or sensitive data, supporting compliance.
- Continuous learning: Models adapt as threats evolve, reducing reliance on static rule sets.
- Enhanced audit trails: AI can reconstruct the entire “life” of a document, identifying who accessed, edited, or shared it—critical for post-breach forensics.
Audit trails and forensics: Tracking the document’s life
Audit trails are the lifeblood of modern document security analysis. Without them, post-mortems turn into guesswork. But not all audit trails are created equal.
Definition list:
A detailed, immutable log detailing every access, modification, or transfer of a document throughout its lifecycle.
The structured process of analyzing audit trails and digital evidence to determine how, when, and why a breach occurred.
Effective document security analysis relies on granular, persistent audit trails that survive even when documents move outside your systems. Blockchain-based logs are gaining traction as a solution, making it nearly impossible for malicious actors to cover their tracks. Leaders who invest in robust forensics capabilities don’t just respond to incidents—they prevent them from recurring.
Document security analysis is only as strong as its weakest audit trail. If you can’t reconstruct who touched what, when, and why, you’re flying blind.
People, culture, and the human firewall
Why tech alone will never save you
Let’s shatter another illusion: there is no firewall strong enough to block human error, indifference, or malice. Technological solutions are vital, but organizations that neglect the human element are doomed to repeat the same mistakes.
“Security isn’t just a technical challenge—it’s a cultural one. The most advanced tools fail in the face of apathy, ignorance, or internal sabotage.”
— Security Awareness Trainer, PaperMark, 2024
- Many breaches start with a single click—phishing, accidental sharing, or credential reuse.
- Security training is not a one-off event; it must be relentless, engaging, and regularly updated.
- Recognition and reward for secure behaviors are often more effective than punitive measures.
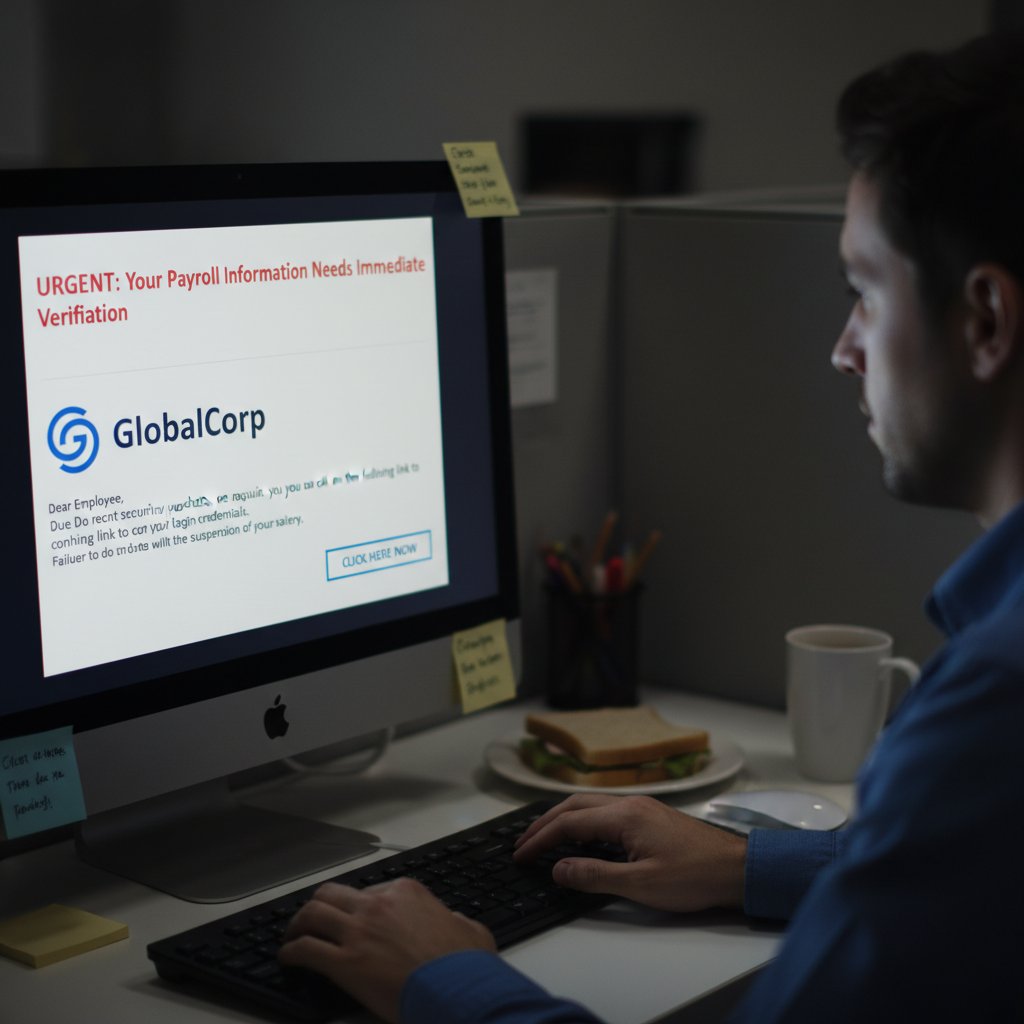
Social engineering: The hacker’s easiest door
Social engineering remains the most efficient tool in an attacker’s kit. No code required—just manipulation and human psychology.
- Phishing: Attackers craft emails mimicking trusted sources to trick employees into sharing credentials.
- Pretexting: Impersonators call or message, posing as IT or HR, extracting sensitive information with authority.
- Baiting: USB drives or links left in common areas, tempting employees to plug in and unleash malware.
- Tailgating: Gaining physical entry by following authorized staff into secure areas.
- Quid pro quo: Offering fake “technical support” in exchange for login details or access.
A single slip can unravel years of technical investment. Document security analysis must address the full human spectrum—trust, fatigue, curiosity, and fear.
Building a security-first culture (and what that really takes)
Transforming culture means more than a policy update or annual training session. It requires relentless communication, leadership buy-in, and a willingness to confront uncomfortable truths—like the fact that not all employees can or will toe the security line.
Foster an environment where reporting suspicious activity is celebrated, not penalized. Make security part of performance reviews, not an afterthought. Invest in regular, creative training that simulates real-world threats—because textbook threats bore, but realistic scenarios stick.
Ultimately, document security analysis is a team sport. The organizations that fare best are those whose people are as vigilant as their technology.
Regulation, compliance, and the global chaos of document laws
Navigating GDPR, CCPA, HIPAA, and the alphabet soup
Document security analysis exists in a swirling vortex of regulations, each with its own requirements and penalties. Leaders must navigate a tangled web: GDPR in Europe, CCPA in California, HIPAA for healthcare, and dozens more worldwide.
| Law | Region | Scope | Maximum Fine |
|---|---|---|---|
| GDPR | EU/EEA | Personal data | €20 million or 4% global revenue |
| CCPA | California, USA | Consumer data | $7,500 per violation |
| HIPAA | USA (healthcare) | Medical info | $1.5 million/year |
| PDPA | Singapore | Personal data | SGD 1 million |
Table 4: Key global document-related data privacy laws and their penalties.
Source: Original analysis based on Varonis, 2024, NU.edu, 2024.
- Identify which regulations apply: Don’t assume—map every jurisdiction.
- Implement controls exceeding minimums: Compliance is a floor, not a ceiling.
- Document your efforts: Regulators love paper trails (digital or otherwise).
- Train staff on local specifics: What’s legal in one region may be criminal in another.
- Review regularly: Laws change; complacency kills.
Where compliance ends and real security begins
Many organizations treat document security analysis as a compliance box to tick. But meeting legal requirements doesn’t guarantee actual safety.
“Compliance-focused security is the bare minimum. Real resilience comes from exceeding those standards, anticipating threats, and testing your defenses constantly.”
— Privacy Officer, Varonis, 2024
The letter of the law won’t save you from a targeted attack—or from reputational damage that regulations don’t cover. Leaders must shift from compliance-driven to risk-driven strategies, using document security analysis as a living process, not a static report.
International wildcards: How global supply chains amplify risk
Your documents don’t respect borders, and neither do your vulnerabilities. Supply chains often stretch across continents, with vendors, partners, and third parties each introducing new vectors for breach.
Data localization laws may require documents to be stored or processed in specific regions—failing to comply can halt operations. Meanwhile, inconsistent standards across vendors can create invisible gaps ripe for exploitation.
Document security analysis must extend beyond your walls. Vet partners rigorously, demand security certifications, and audit their processes as ruthlessly as your own. When everyone’s responsible, no one is accountable—unless you enforce it.
Action plan: How to bulletproof your document security strategy
Step-by-step guide to conducting a document security analysis
A thorough document security analysis isn’t a one-and-done task. Here’s a stepwise, research-backed approach:
- Inventory all documents: Catalogue sensitive files, their locations, access controls, and movement.
- Map workflows: Understand how documents flow between people, departments, and systems—including informal “shadow IT” channels.
- Assess vulnerabilities: Review existing defenses, audit trails, and historical incidents for common failure points.
- Test controls: Run penetration tests, phishing simulations, and red team exercises targeting document processes.
- Review compliance: Cross-reference with laws and policies relevant to every jurisdiction you operate in.
- Train staff: Deliver tailored training addressing both technical and social engineering threats.
- Monitor and adapt: Use real-time analytics and AI-driven tools to catch new risks as they emerge.
Critical mistakes to avoid (and how to fix them)
- Ignoring insider risk: Don’t fixate on external hackers to the exclusion of internal threats.
- Over-reliance on legacy tools: “Set and forget” document controls are outpaced by modern attack techniques.
- Treating compliance as a finish line: Laws change, and minimum standards won’t stop targeted attacks.
- Failing to map the full document lifecycle: Leaks don’t just happen at endpoints—review every step.
- Neglecting regular training: One-and-done security briefings fade fast; make it ongoing.
Fix these by embracing continuous improvement, investing in platforms like textwall.ai, and prioritizing both people and process alongside technology.
Checklists and quick wins: Start securing documents today
- Map your most sensitive documents—know what’s at stake.
- Review and tighten user permissions; “need to know” should be more than a cliché.
- Enable robust encryption for both storage and transmission.
- Implement watermarking and digital signatures for critical files.
- Set up automated alerts for unusual access or sharing behaviors.
- Schedule regular, realistic security awareness training.
- Audit third-party vendors for compliance and security controls.
| Checklist Item | Impact Level | Frequency |
|---|---|---|
| Inventory sensitive documents | High | Monthly |
| Review access permissions | High | Quarterly |
| Staff training | Medium | Quarterly |
| Vendor audits | High | Annually |
| Penetration testing | High | Annually |
Table 5: Core document security tasks and recommended frequencies.
Source: Original analysis based on Exabeam, 2024, PaperMark, 2024.
Case files: Real-world wins and horror stories
The hospital that dodged a disaster (barely)
In early 2024, a major hospital discovered that thousands of patient records were exposed via an unsecured shared drive. The breach was caught by a junior IT analyst performing a routine audit—no AI, no advanced forensics, just a sharp eye and a healthy dose of skepticism. The immediate fallout was contained, and no data appears to have been stolen. Post-incident analysis revealed the breach resulted from a misconfigured permission set after a software update, and the quick response prevented regulatory fines and reputational disaster. The lesson: low-tech vigilance still matters, and document security analysis should empower everyone to spot the unusual.
The hospital responded by implementing real-time usage analytics—boosting insight into document access by 90%, echoing industry trends (PaperMark, 2024).
When AI saved the day—and when it made things worse
AI-powered document analysis isn’t a silver bullet, but it can be transformative. In one case, a manufacturing firm using AI flagged a subtle anomaly—a contract revision that introduced hidden, malicious code. The threat was neutralized before any harm was done.
But the same technology can amplify mistakes. Another organization’s overzealous AI locked out staff from critical documents after misclassifying them as “high risk” during an urgent project. Productivity tanked, delays mounted, and trust in the system eroded.
- AI excels in spotting the unseen: pattern anomalies, metadata mismatches, and suspicious sharing.
- But poorly tuned models can trigger false positives, causing operational chaos.
- Human oversight is non-negotiable: automation without accountability is just as dangerous as complacency.
User testimonials: What leaders wish they’d known
Seasoned leaders share a recurring theme: document security analysis is about humility, not hubris.
“If I could go back, I’d invest in staff training and real-time analytics before throwing money at the latest tech. Tools matter, but people make or break your system.”
— Operations Director, Manufacturing, PaperMark, 2024
Leaders who treat document security analysis as a cultural priority, not just a technical one, report greater resilience and fewer catastrophic breaches. The takeaway: “Trust, but verify—at every level.”
The future of document security analysis: AI, zero trust, and what’s next
Disruptive trends you can’t ignore
Document security analysis is in flux, but some trends are already reshaping the battlefield:
- Zero trust architectures: Treating every document, user, and device as untrusted until proven otherwise.
- Generative AI-driven attacks: Deepfake documents and synthetic identities complicate verification.
- Blockchain adoption: Immutable audit trails for vital agreements and sensitive records.
- Decentralized identity management: Moving away from central authorities to distributed trust models.
- Converged compliance tools: Integrating document and data security, analytics, and legal tracking into unified platforms.
Zero trust: Hype or salvation?
Zero trust is more than a buzzword—it’s a fundamental rethinking of trust in the digital age. The philosophy: never trust, always verify, at every interaction.
| Zero Trust Element | Traditional Security | Zero Trust Approach |
|---|---|---|
| Network boundary | Trusted inside | No implicit trust |
| User authentication | Periodic login | Continuous verification |
| Access control | Role-based, static | Dynamic, context-aware |
| Document sharing | Perimeter-based | Granular, conditional |
Table 6: How zero trust compares to traditional document security methods.
Source: Original analysis based on PaperMark, 2024.
Zero trust isn’t hype—it’s an adjustment to the realities of modern threats. But it requires organizational buy-in and significant operational change.
Zero trust, like AI, isn’t a panacea—it’s a mindset shift. The organizations thriving today are those that embed this philosophy in both technical and cultural practices.
Preparing for tomorrow’s threats—today
- Assess your document security posture against emerging attack vectors—don’t wait for an incident to force your hand.
- Invest in continuous monitoring and real-time analytics; static reports are obsolete.
- Train your teams to recognize and respond to new threats, from deepfakes to AI-generated phishing.
- Regularly test your defenses, simulating both insider and outsider attacks.
- Collaborate with peers, vendors, and regulators—collective intelligence outpaces solo efforts.
Document security analysis isn’t a destination; it’s an arms race. The only way to stay ahead is to treat every day as day one.
Beyond the obvious: Adjacent threats and radical ideas
Insider threats nobody wants to talk about
Some insider threats are taboo: senior executives with unchecked access, third-party contractors with privileged credentials, or “trusted” partners operating outside your direct oversight. Document security analysis must pierce the veil of hierarchy and convenience—no one gets a free pass.
Some organizations have uncovered massive leaks only after years of trusted insiders siphoning data, sometimes unintentionally, sometimes for personal gain. These failures often stem from:
- Overly broad permissions for senior staff—“too important to restrict.”
- Lack of monitoring for privileged accounts—“they’d never risk it.”
- Blind spots in third-party integrations—“we trust our partners.”
The solution: ruthless role segmentation, mandatory monitoring, and a culture that values security over status.
Unconventional document security tactics from espionage to enterprise
Sometimes, the boldest tactics are found outside the boardroom. Espionage agencies have long used counter-surveillance, “canary traps,” and even decoy documents to catch leakers.
- Deploying “honey documents” with unique watermarks to detect unauthorized access.
- Staggered document versions—feeding different stakeholders slightly altered copies to pinpoint leaks.
- Physical security sweeps for unexplained printouts or USB drives.
- Biometric access for the most sensitive files—iris scans for top executives, for example.
Most organizations don’t need spy-level countermeasures, but thinking creatively—beyond compliance—can turn the tables on persistent threats.
The role of AI in shaping tomorrow’s document landscape
AI isn’t just a tool; it’s an ecosystem. From real-time risk scoring to signature verification and anomaly detection, AI-driven document security analysis is already outperforming human-centric processes on both speed and accuracy.
But AI also introduces new risks—amplifying errors, perpetuating bias, and creating attack surfaces that didn’t exist before. As PaperMark, 2024 notes, “AI in document security is only as strong as the data and oversight feeding it.”
“The AI arms race is here—defenders and attackers both wielding smarter tools. Leaders who treat AI as an ally, not a replacement, are the ones who’ll still be standing.”
— Senior Security Researcher, PaperMark, 2024
Conclusion
Document security analysis isn’t a technical footnote—it’s the frontline of trust, reputation, and business survival. The brutal truths are clear: threats evolve daily, compliance is just a starting point, and your biggest risks often walk the halls with a badge. Addressing document security means sweating every detail—technology, process, people, and culture—with relentless honesty. Platforms like textwall.ai are helping organizations stay ahead, but the real work happens every day, in every department, by every employee. The cost of complacency is headline news. Don’t just check the box—own your document security analysis and let no brutal truth catch you off guard.
Sources
References cited in this article
- PaperMark(papermark.com)
- SpringerLink(link.springer.com)
- Exabeam(exabeam.com)
- Varonis(varonis.com)
- NU.edu(nu.edu)
- QRMark(qrmark.com)
- EvaluationGrid(evaluationgrid.co)
- NTE.ai(nte.ai)
- Cobalt(cobalt.io)
- ENISA Threat Landscape 2024(op.europa.eu)
- Trend Micro(trendmicro.com)
- AztechIT(aztechit.co.uk)
- F-Secure Scam Intelligence Report 2024(f-secure.com)
- WEF Global Cybersecurity Outlook 2024(www3.weforum.org)
- Varonis(varonis.com)
- CSIS(csis.org)
- ITRC(securityboulevard.com)
- NY Times(nytimes.com)
- IBM Insider Threats 2024(ibm.com)
- StationX(stationx.net)
- Edge Delta(edgedelta.com)
- SHRM(shrm.org)
- Forbes(forbes.com)
- IAEE(iaee.com)
- Compliance & Risks(complianceandrisks.com)
- Thomson Reuters(thomsonreuters.com)
- Secureframe(secureframe.com)
- Accutive Security(accutivesecurity.com)
- Plurilock(plurilock.com)
- Federal Register(federalregister.gov)
- WEF Global Risks Report 2024(weforum.org)
- Xeneta(xeneta.com)
- DHL/Everstream(dhl.com)
- IBM(secureframe.com)
- Adobe Blog(blog.adobe.com)
Ready to Master Your Documents?
Join professionals who've transformed document analysis with TextWall.ai
More Articles
Discover more topics from Advanced document analysis

Document Search Optimization in 2026: Stop Losing Work in Plain Sight
Document search optimization is broken. Discover the 9 truths sabotaging your workflow—and the breakthrough strategies you need in 2026. Don’t fall behind. Read now.

Document Scanning Technology in 2026: Asset or Liability?
If you still think document scanning technology is just a “nice-to-have” for your business, you’re living in a paper-fueled fever dream. In 2025, the stakes

Document Scanning Solutions Comparison That Exposes 2026’s Real ROI
Discover 2026’s hard truths, hidden costs, and game-changing features. Get the real story before you make your next move.

Document Scanning Software Reviews 2026 That Actually Save You Time
Document scanning software reviews for 2026: Cut through hype with edgy, in-depth analysis, real-world case studies, and surprising truths—find the right tool now.

Document Scanning Services Comparison for 2026: 11 Costly Myths
Discover insights about document scanning services comparison

Document Scanning Services in 2026: Roi, AI Risks and Real Wins
Unmask myths, hidden risks, and AI-powered breakthroughs. Get the definitive 2026 guide to digital transformation—act before your data disappears.

Document Scanning Best Practices That Prevent Million‑dollar Mistakes
Document scanning best practices for 2026: Discover brutal truths, avoid hidden pitfalls, and master flawless results—take control of your digital transformation now.

Document Scanning Automation in 2026: Roi, Risks and Real Wins
Document scanning automation is transforming business in 2026. Expose hidden risks, discover real ROI, and master workflow hacks. Don’t get left behind—read now.

Document Scanning Accuracy Improvement When Errors Cost Millions
Document scanning accuracy improvement starts here. Discover hidden risks, bold solutions, and expert-backed fixes—don’t let errors cost you big. Read now.